Hub-spoke is the standard Azure networking pattern. Microsoft recommends it, the Cloud Adoption Framework prescribes it, and every architecture diagram you've seen has a hub VNet in the middle with spokes radiating outward.
What nobody talks about is how much the hub costs.
We review a lot of Azure environments, and the hub subscription is consistently one of the most expensive parts of the estate — yet it gets the least scrutiny. It's "infrastructure." It's "just networking." It was set up during the initial landing zone deployment and hasn't been questioned since. That's exactly why it's quietly burning thousands of pounds every month.
The Real Cost of a Hub Subscription
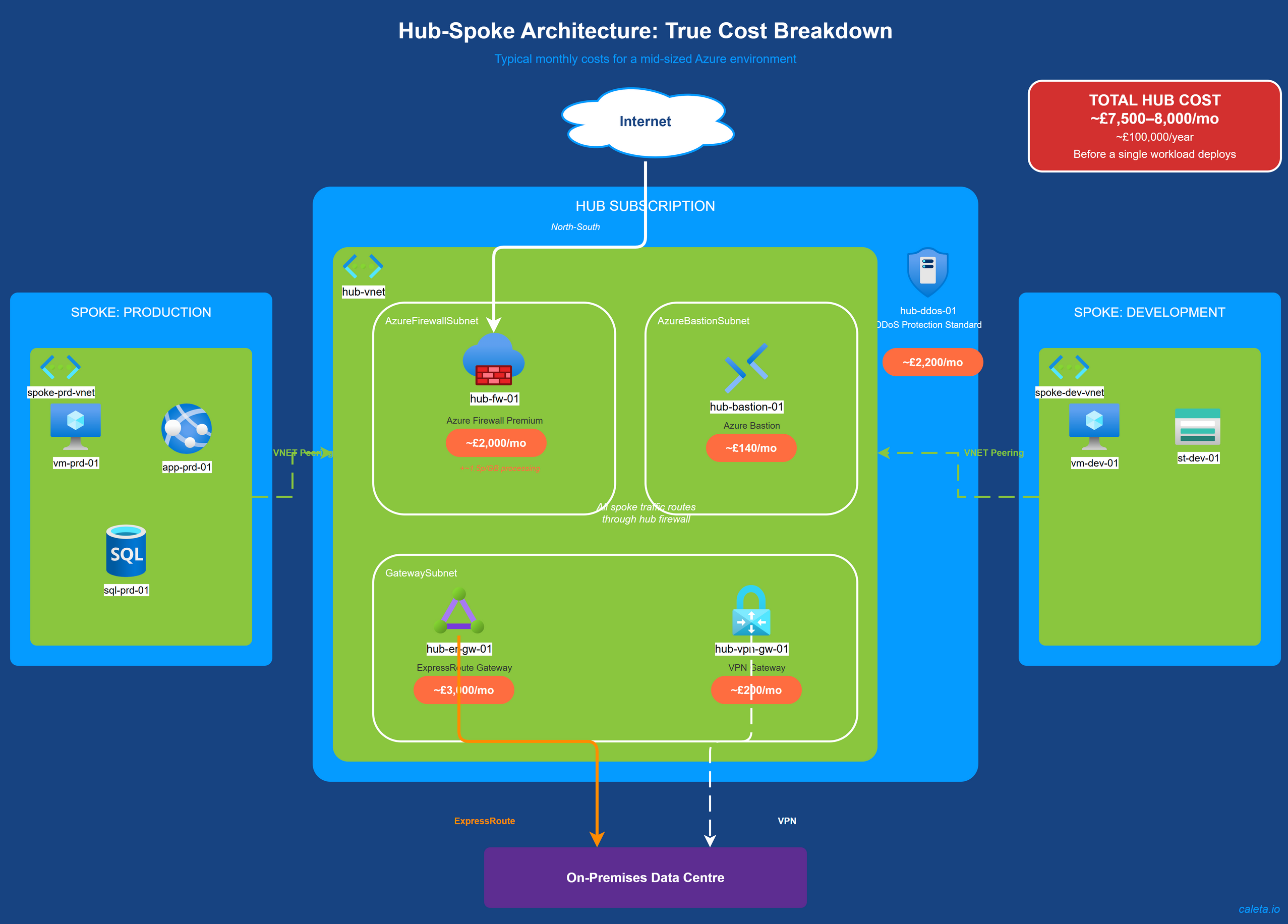
Here's what a typical hub subscription looks like. These are the numbers we commonly see across mid-sized environments:
- Azure Firewall (Premium): ~£2,000/month
- ExpressRoute circuit: ~£3,000/month
- VPN Gateway: ~£200/month
- DDoS Protection Standard: ~£2,200/month
- Azure Bastion: ~£140/month
That's £7,500–£8,000 a month. Just for the hub. Before a single spoke workload is deployed.
Roughly £100,000 a year on infrastructure plumbing that most organisations treat as an unchangeable fixed cost.
Azure Firewall: The Biggest Line Item
Azure Firewall is usually the single largest cost in the hub.
The base deployment fee alone is substantial — Standard runs at ~£1,100/month, Premium at ~£2,200/month. That's just to have the firewall deployed and running, before any traffic flows through it.
Then there's data processing. Every gigabyte routed through the firewall incurs ~1.5p/GB. That sounds trivial until you consider that hub-spoke architectures route all traffic through the hub. A busy environment pushing several terabytes a month can easily add hundreds of pounds on top of the base fee.
Premium vs Standard: Paying for Features You Don't Use?
This is one of the most common waste patterns we see. An organisation deployed Premium because it was recommended during initial architecture design, and nobody has revisited the decision since.
Azure Firewall Premium adds three capabilities over Standard:
- TLS inspection — decrypts and inspects encrypted traffic
- IDPS — signature-based threat detection
- Enhanced URL filtering — more granular URL-based rules
Genuinely valuable features — if you're actually using them.
TLS inspection requires significant configuration: certificate management, traffic selection, exemptions for services that don't work well with TLS termination. If that configuration hasn't been done, TLS inspection isn't active — and you're paying Premium pricing for Standard functionality.
We regularly find environments where Premium is deployed but none of the Premium-exclusive features are configured. That's ~£1,000/month in pure waste.
DDoS Protection: The Flat Fee That Stings
DDoS Protection Standard costs ~£2,200/month as a flat fee covering up to 100 public IP addresses. Excellent value if you have dozens of public-facing resources.
But if you only have a handful of public IPs? You're paying over £2,000/month to protect three or four addresses.
DDoS IP Protection is priced per public IP rather than as a flat fee. For organisations with fewer than ~15 public IPs, this tier can be dramatically cheaper. We've seen organisations cut this line item by 80% just by switching tiers.
Alternatives Worth Considering
Azure Firewall isn't the only option for controlling traffic in a hub-spoke architecture.
NSGs and UDRs are free. Not a like-for-like replacement for a stateful firewall, but for basic traffic control — allow/deny by source, destination, port, protocol — they're often sufficient. Many organisations use Azure Firewall for traffic that NSGs could handle.
Azure Firewall Basic is aimed at smaller environments. At ~£250/month, it's a fraction of Standard's cost. For non-production environments or development hubs, Basic often delivers what's needed.
Third-party NVAs (Palo Alto, Fortinet) running on Azure VMs can be more cost-effective at scale, particularly with existing licensing agreements. The trade-off is operational complexity — managing VMs and appliance software rather than consuming a managed service.
Hybrid approaches are often the smartest option. Use NSGs for east-west traffic between spokes and reserve Azure Firewall for north-south traffic where you need stateful inspection and centralised logging. This significantly reduces firewall data processing charges.
The Hub Is Not Sacred
The hub-spoke pattern is sound architecture. We're not arguing against it. What we are arguing against is treating the hub as an untouchable fixed cost.
Every service in the hub is a configuration choice, and every choice has alternatives. Premium can be Standard. Standard can be Basic. DDoS Standard can be IP Protection. NSGs can replace firewall rules for certain traffic patterns. These aren't radical changes — they're the same right-sizing exercises you'd apply to any other resource.
The difference is that nobody thinks to apply them to the hub. And that's why it quietly becomes one of the most expensive parts of your Azure estate without anyone noticing.
Not sure whether your hub-spoke architecture is costing more than it should? Request a FinOps assessment — we'll break down your networking spend and show you where the savings are.